Ethical Hacking: A Beginner’s Guide to Cybersecurity
Ethical Hacking Guide for Beginners in 2026

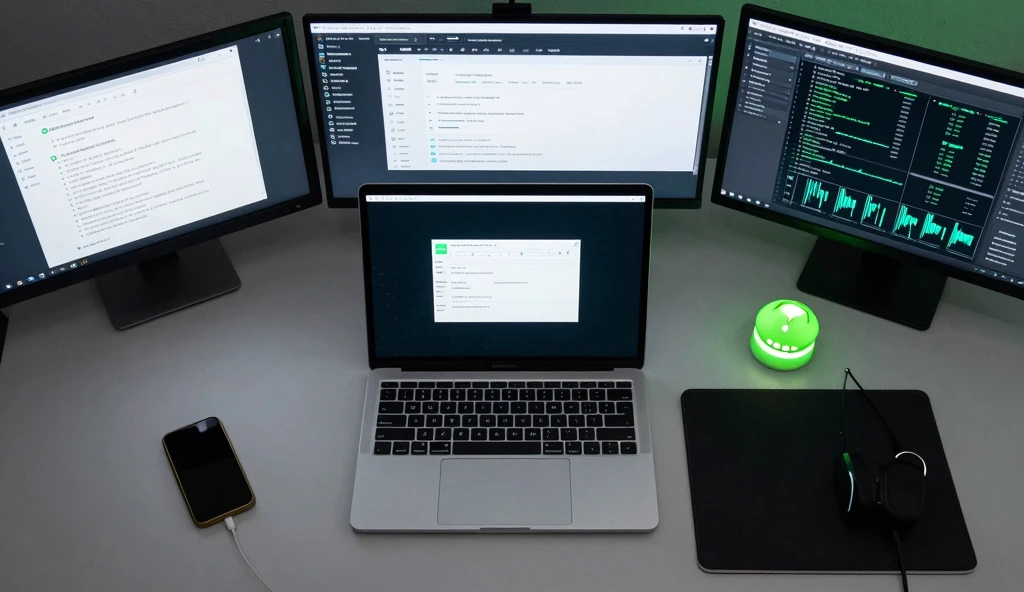
Threats prevail in the digital world today. Every day, individuals, companies, and states go online for communication, business, and services. As more systems move online, attackers also increase in number. However, not every hacker aims to cause harm. In fact, many skilled professionals step in to identify system vulnerabilities before malicious individuals exploit them. This valuable practice is known as ethical hacking. In this guide, you will learn what ethical hacking is, how it operates, the tools frequently used, as well as how to become one.
What Is Ethical Hacking?
Ethical hacking involves testing networks and computer systems to identify security vulnerabilities. Unlike criminal hackers, ethical hackers control their activities and follow strict legal boundaries. Organizations hire them to strengthen digital defenses. The goal remains simple: uncover loopholes before bad actors or malicious software exploit them.
To clarify further, an ethical hacker never accesses systems for personal gain. Instead, they use their technical abilities for protection and improvement. For this reason, people often refer to them as white hat hackers.
Why Ethical Hacking Matters
Cyber attacks can ruin any organization. For example, stolen databases expose personal information. Likewise, ransomware locks vital systems and disrupts operations. As threats continue to grow, ethical hackers provide essential protection.
Additionally, white hat hacking:
-
Improves digital trust
-
Prevents costly breaches
-
Supports safe software development
-
Helps firms comply with regulations
Because of these advantages, businesses now actively build ethical hacking teams to secure their systems.
The History of Ethical Hacking: Interest to Profession
Initially, ethical hacking did not exist as an official profession. In the early days of computing, many hackers experimented with systems simply to explore their capabilities. Over time, organizations realized that curious and skilled minds could protect infrastructure instead of threatening it.
Gradually, ethical hacking evolved into an established field. Today, it forms a crucial part of cybersecurity strategies in modern companies. Governments, technology firms, and security teams rely on ethical hackers daily to identify threats before they affect users.
Types of Hackers (The Good, The Bad, and The Unknown)
Understanding ethical hacking begins with recognizing different types of hackers:
White Hat Hackers
These professionals practice ethical hacking. They test systems legally, identify vulnerabilities, and report problems so organizations can fix them.
Black Hat Hackers
In contrast, black hat hackers seek personal gain. They break into systems, steal data, or disrupt services. As a result, they cause serious harm to individuals and organizations.
Grey Hat Hackers
Grey hat hackers operate between white and black hats. Sometimes, they discover vulnerabilities without permission and later report them. Although they may not intend harm, they still act in a legally risky space.
The Nuts and Bolts of Ethical Hacking
Ethical hacking follows a clear and procedural approach. Most professionals use a structured method to identify and correct risks efficiently.
Permission First
First and foremost, ethical hackers obtain written consent from the system owner. This step protects both parties and prevents legal complications.
Planning and Reconnaissance
Next, the hacker collects information about the system. This includes IP addresses, open ports, and visible services. At this stage, they only observe and gather data without deep interaction.
Scanning
After gathering initial data, ethical hackers use tools to scan the system. Through scanning, they identify weak points while ensuring system stability.
Gaining Access
Then, ethical hackers attempt to exploit the discovered vulnerabilities. If they succeed, they demonstrate the presence of a real security threat.
Maintaining Access
At this stage, ethical hackers evaluate how long an attacker could remain inside the system without detection. Consequently, organizations understand the severity of the risk.
Reporting
Finally, ethical hackers prepare a detailed report. They explain what they discovered, how they discovered it, and how to fix it. This report serves as a roadmap for improving overall security.
Typical Tools of Hackers Ethics
Ethical hackers use numerous tools to test systems effectively. Each tool serves a specific purpose in the testing process.
-
Nmap – maps open ports and services
-
Wireshark – analyzes network traffic
-
Metasploit – tests exploitation frameworks
-
Burp Suite – scans web application vulnerabilities
-
Kali Linux – provides a complete hacking operating system with built-in tools
Through these tools, ethical hackers uncover issues that manual inspection might miss.
Skills Every White Hat Hacker Must Have
To succeed, ethical hackers must combine technical expertise with analytical thinking. Essential skills include:
-
Networking fundamentals
-
Linux command line expertise
-
Python and Bash programming knowledge
-
Database administration (SQL)
-
Understanding of encryption
-
Strong problem-solving mindset
-
Attention to detail
Over time, practice strengthens these abilities. Moreover, many ethical hackers use online labs and simulations to improve skills safely.
Certifications to Increase your Credibility
Certifications help ethical hackers stand out in the competitive job market. Popular examples include:
-
CEH (Certified Ethical Hacker) – widely recognized certification
-
CompTIA Security+ – entry-level cybersecurity credential
-
OSCP – hands-on penetration testing certification
These certifications show employers that you understand core concepts and follow ethical standards.
Ethical Hacking Career Paths
Ethical hacking offers flexible and rewarding career opportunities. Common roles include:
-
Penetration Tester – identifies system vulnerabilities
-
Security Analyst – monitors and protects systems
-
Cybersecurity Consultant – advises organizations on risk management
-
Bug Bounty Hunter – discovers and reports vulnerabilities for rewards
Because demand continues to rise, professionals in this field often earn competitive salaries.

Difficulties Facing Ethical Hackers
Although ethical hacking offers many benefits, it also presents challenges. For example:
-
Staying updated with emerging threats
-
Avoiding legal issues without proper permission
-
Managing complex and large systems
-
Handling pressure to resolve vulnerabilities quickly
Nevertheless, ethical hackers who remain curious and adaptable continue to thrive in this dynamic field.
Conclusion: Reason Why Ethical Hacking Will Remain Relevant
In conclusion, ethical hacking plays a vital role in defending the digital world. As cyber threats increase, organizations seek professionals who think like attackers yet act with integrity. Therefore, ethical hacking will remain essential for years to come. If you enjoy problem-solving and security, this career path offers both excitement and purpose.




